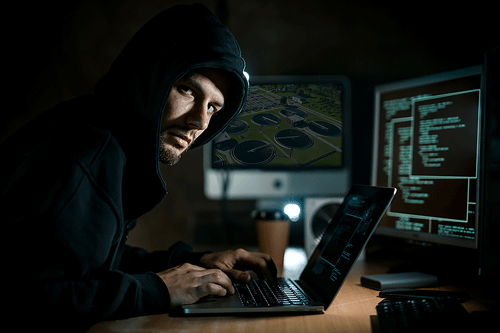
While cybersecurity threats to the water sector are not new, the digital transformation of utilities has increased the risks exponentially. One of the biggest cybersecurity hazards facing water companies and all critical infrastructure organizations is the possibility of an attacker taking control of their information technology (IT) or operational technology (OT) systems to steal data and block or disrupt operations. Many of the risks utilities are facing also stem from the continued use of legacy systems, which were installed many years ago. These systems often have minimal, if any, cybersecurity features and present a digital attack surface.
As if these challenges were not enough for water utilities, the Environmental Protection Agency (EPA) recently unveiled new federal mandates requiring states to expand inspections of water systems to include cybersecurity threats. What this ultimately means is that states already responsible for inspecting everything from tanks to pumps and operations at hundreds of public water systems (PWSs) across the nation would also need to ensure utilities are protected against hackers.
The plan, which has been debated for almost a year, has fueled concerns in the water sector about the ability of cash-strapped states with limited cyber expertise to shoulder such a hefty and quickly evolving responsibility. While the White House earmarked $2 billion from the bipartisan infrastructure bill that was signed into law in 2022 to go toward strengthening United States infrastructure against cyberattacks, this new requirement could have an effect on water utilities’ capital expenditure (capex) budgets, and margins would be pressured if systems are unable or unwilling to pass on the added costs to customers through rate increases.
Fitch Ratings said this will add an increased regulatory and financial burden, which could be onerous for smaller systems and systems with minimal existing cyber infrastructure.1 They added, “Water utility operational technology can be quite old and may not be compatible with needed cybersecurity upgrades or software enhancements. We expect water utilities could incur significant costs in the medium term to update systems and upgrade infrastructure to improve cybersecurity.”2
Bluefield Research recently reported from the 2023 American Water Works Association Utility Management Conference that utilities are still processing the implications of the EPA’s new cybersecurity audits and sanitary survey (periodic audits of water systems) completion. An IT cultural shift is underway in many cities, as they become more reliant on cloud services and overcome their fears of hacked supervisory control and data acquisition (SCADA) systems or ransomed billing platforms.3
Surveying & Reporting Requirements
The EPA regulation states water utilities can conduct a self-assessment or have it done by an approved third-party resource such as a Cybersecurity and Infrastructure Security Agency (CISA) cybersecurity adviser through the EPA’s water sector cybersecurity evaluation program, or a private sector technical assistance provider that has state approval. Currently, the only approved third-party assessment resources are limited to the Department of Homeland Security, EPA and states, which makes this activity hard to scale across the breadth of water utilities across the country.4
The goal of sanitary surveys is to ensure states effectively identify deficiencies and PWSs then correct those deficiencies—including cybersecurity-related weaknesses—that could impact safe drinking water. To help with this, the EPA is offering considerable technical assistance and support to states and PWSs to help close cybersecurity gaps.5
In addition to working with the EPA, utilities of any size can also create the required reports through third-party software that seamlessly integrates with programmable logic controllers (PLCs), SCADA and historian systems. These reports are generated in a spreadsheet format to meet the regulatory requirements and determine the compliance of the treatment system and if any security breaches occurred. Regulatory reporting requires a combination of process and manually entered data, derived calculations and displaying the data in nontabular formats. Innovative companies have developed robust software that combines the flexibility of spreadsheet programs with powerful automated data collection to handle the entire process with ease.
Compromised Systems
Identifying deficiencies for cybersecurity should include the absence of a practice or control, or the presence of a vulnerability, that has a high risk of being exploited, either directly or indirectly, to compromise an operational technology used in the treatment or distribution of drinking water. For example, the smart sensors that are connected to pumps and pump systems to automate and modernize the water-based process create new exploitable entry points for cybercriminals to manipulate remotely and move laterally within the systems.6
There are myriad worst-case scenarios about what a threat actor could do to a water system. One example is that sophisticated actors could hack a system and manipulate pumps or chemical feeds without the utility even knowing they were in the system.
Support
The EPA is committed to partnering with the states to ensure all PWSs adopt cybersecurity practices that are essential to protecting public health. To that end, the Department of Homeland Security (DHS) announced a cybersecurity grant program specifically for state, local and territorial (SLT) governments across the country. Funding from the State and Local Cybersecurity Grant Program (SLCGP) and the Tribal Cybersecurity Grant Program (TCGP) helps eligible entities address cybersecurity risks and threats to information systems owned or operated by—or on behalf of—SLT governments.
These entities face unique challenges in defending against cyber threats such as ransomware, as they lack the resources to defend against constantly changing threats. DHS, through the CISA, is taking steps to help stakeholders across the country understand the severity of their unique local cyber threats and cultivate partnerships to reduce related risks across the SLT enterprise.7
Additionally, on April 4, 2023, the EPA announced over $6.5 billion for states, tribes and territories for essential drinking water infrastructure upgrades across the nation through the Drinking Water State Revolving Fund (DWSRF).
Preparing for the Future
The Water and Wastewater Systems Sector provides essential services that support the operation of all U.S. critical infrastructure. Water and wastewater facilities rely on IT and OT systems to operate, and a compromise of these systems could lead to disruptions of service and cascading impacts throughout U.S. critical infrastructure.8
While the new ruling is getting some pushback, the EPA is offering technical assistance and support to states in this effort, as well as to PWSs to help close cybersecurity gaps. Clarifying cybersecurity must be evaluated during sanitary surveys or other state programs when reviewing operational technology that is part of a PWS equipment or operation will help reduce the likelihood of a successful cyberattack on a PWS and improve recovery if a cyberincident occurs.
References
eenews.net/articles/federal-cyber-mandate-looms-for-local-water-systems/ (accessed June 13, 2023).
Ibid
bluefieldresearch.com/finding-the-fit-water-utilities-adjust-to-ongoing-challenges/ (accessed June 13, 2023).
cyberscoop.com/epa-water-cyber-regulations/ (accessed June 13, 2023).
epa.gov/system/files/documents/2023-03/230228_Cyber%20SS%20Guidance_508c.pdf (accessed June 14, 2023).
https://blog.scadafence.com/water-utilities-face-increasing-risk-of-cyber-attacks (accessed June 14, 2023).
cisa.gov/state-and-local-cybersecurity-grant-program (accessed June 14, 2023).
cisa.gov/topics/critical-infrastructure-security-and-resilience/critical-infrastructure-sectors/water-and-wastewater-sector (accessed June 14, 2023).

